Avoiding a New Single Point of Failure: Designing Distributed Safety Enforcement
Blog Series: The Death of Static Safety This is the third part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive...
4 min read
 Michael Entner-Gómez
:
Feb 20, 2026 8:32:00 AM
Michael Entner-Gómez
:
Feb 20, 2026 8:32:00 AM

Table of Contents
This is the second part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive into the following topic of validating operational assurance as a safety mechanism and who exactly is watching the "watcher".
To read part one of this series, we invite you to do so. Let's dive in!
Once the limits of static safety are acknowledged, the next objection follows naturally: if operational assurance influences system behavior, how can the monitor itself be trusted?
This is the correct question. Any mechanism that can constrain, override, or transition an autonomous system becomes part of the safety chain. Treating such a mechanism as advisory analytics or post-hoc reporting is not just inaccurate, it is unsafe.
Operational assurance either belongs in the safety architecture, or it does not belong at all.
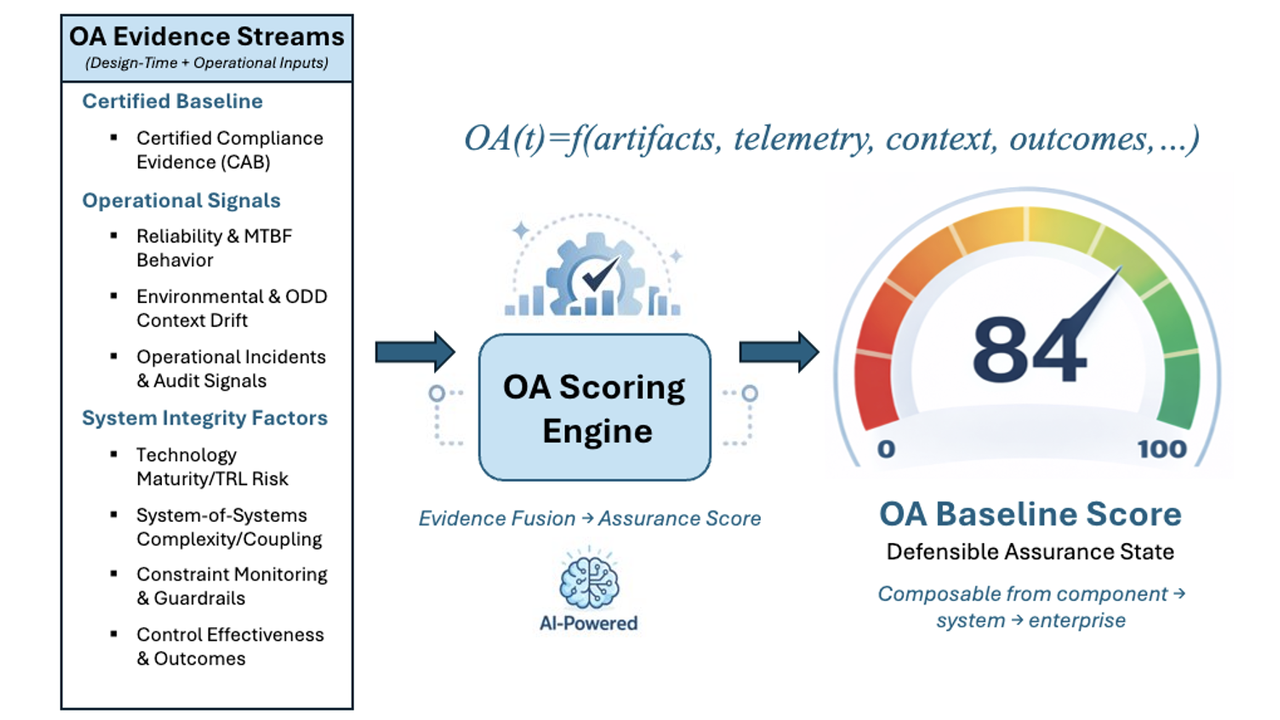
There is a persistent misconception that an Operational Assurance System is simply a scoring engine that flags risk. That framing avoids the hard work of safety analysis, but it also avoids reality.
The moment an assurance mechanism influences behavior, whether by constraining autonomy, triggering a fallback, or enforcing an operational boundary, it is no longer observational. It is supervisory control.
At that point, the question is not whether the system is useful. The question is whether it meets the same standards applied to every other safety-related function in the vehicle.
If it cannot, it does not belong in the loop.
Discussions about assurance often fail because they start from the wrong premise. The question is framed as whether the monitor itself can be trusted as a complex, holistic system. That leads directly to unbounded reasoning and arguments that cannot be certified.
This is not how safety validation works.
ISO 26262 does not require trust in emergent behavior. It requires traceability, bounded logic, and evidence. Operational assurance is validated the same way any other safety mechanism is validated, not as a monolithic intelligence, but as a collection of certified constraints.
Every enforced condition must be traceable back to hazards identified in the HARA (ISO 26262) and the SOTIF analysis (ISO 21448). Every enforcement action must be deterministic, testable, and bounded. There can be no reliance on opaque scoring, adaptive policies, or learning-based behavior in the enforcement path.
The safety claim is not “trust the monitor.”
The safety claim is that certified constraints are implemented as verifiable runtime safety guards.
This distinction between analysis and enforcement is essential.
Complex analytics, inference, and statistical assessment can play a valuable role in understanding operational risk. They can inform engineering decisions and support continuous improvement. What they cannot do is directly command safety-critical actions.
The enforcement layer must be simple by design. Its behavior must be predictable under fault conditions. Its failure modes must be understood. Its actions must be explicitly linked to pre-analyzed hazards and pre-certified safe operational states.
Emergent behavior may be acceptable in performance functions. It is not acceptable in safety mechanisms. Bounded logic is not a limitation. It is what makes certification possible.

Why OAS belongs in the safety chain: A comparison between deterministic
safety supervisors and probabilistic analytics/monitoring tools.
Once operational assurance is treated as a safety mechanism, familiar requirements apply.
It must be traceable to safety requirements derived from the HARA and SOTIF analysis. It must be verified with the same rigor as other supervisory functions. It must meet appropriate ASIL expectations for independence, coverage, and fault tolerance. It must fail safely.
This reframing eliminates the false debate about whether assurance systems are “too complex to trust.” Complexity is not trusted in safety. Constraints are.
If the enforcement logic cannot be fully specified, tested, and justified, it does not belong in the safety path. If it can, then it is validated in exactly the same way as braking supervision or steering arbitration.
Another common concern is that operational assurance introduces a new safety argument that must be defended independently. That concern misunderstands its role.
Operational assurance does not create a parallel safety case. It extends the existing one into operational time. The hazards do not change, but the triggering events do. Operational assurance provides evidence that the system's performance and functional adequacy remain valid in an evolving Operational Design Domain (ODD). The safety goals do not change. The safe states do not change.
What changes is that there is now evidence that the assumptions underpinning those claims continue to hold after deployment.
Without that evidence, the safety case slowly detaches from the system as it actually operates. With it, the safety argument remains anchored to reality.
The real danger is not that operational assurance becomes too powerful. The real danger is that it is treated as a non-safety add-on because validating it feels uncomfortable.
Avoiding safety classification does not reduce risk. It hides it.
Any system that influences behavior without being held to safety standards creates an unexamined control path. That is precisely the type of latent hazard functional safety is meant to prevent.
Operational assurance must therefore be designed to earn its place in the safety architecture, or it must be excluded entirely.
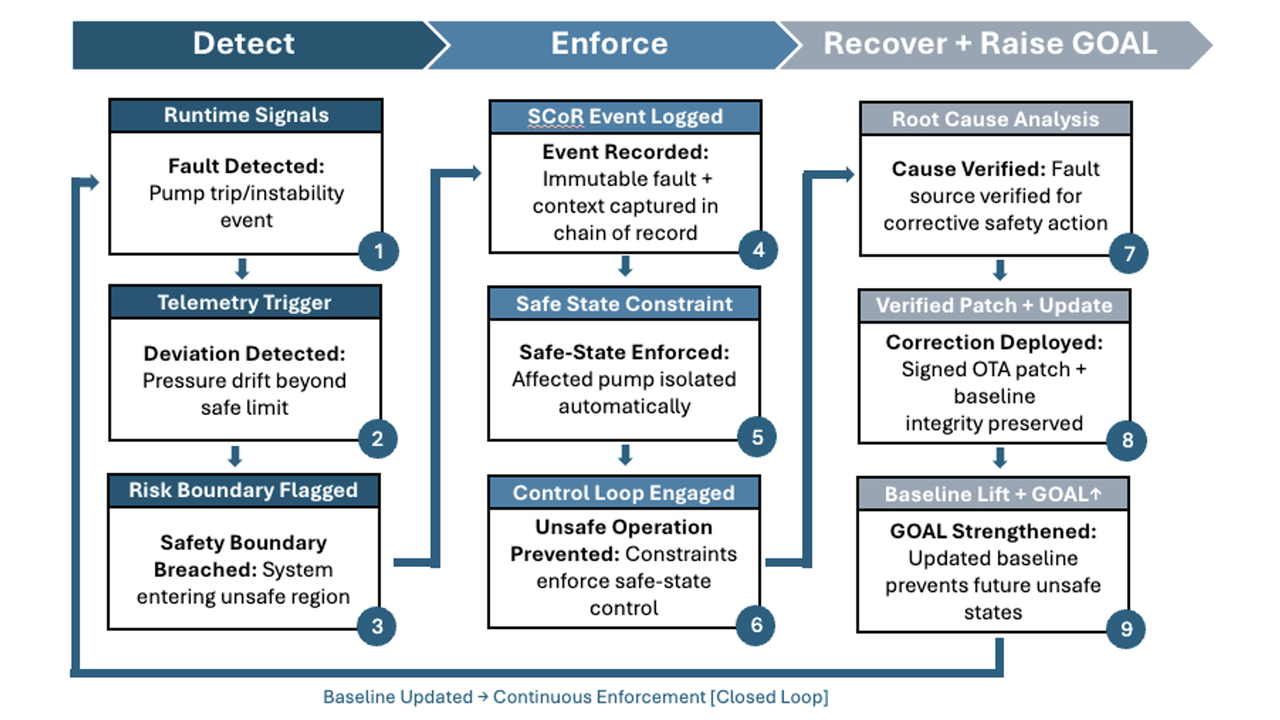
In the next article, the focus shifts from validation to architecture. Even a correctly validated assurance mechanism can fail certification expectations if it becomes a new single point of failure. The question then becomes how runtime enforcement can be distributed, redundant, and fail-safe by design.
LHP Operational Assurance Systems (OAS) was spun out of LHP Engineering Solutions to address a growing gap in safety-critical, software-defined systems: certification at launch no longer guarantees safe operation over time. As complex platforms began receiving continuous software updates and evolving functionality, LHP OAS recognized that traditional "certify-once" models could not prevent runtime drift between validated safety intent and real-world behavior. Drawing on decades of leadership in functional safety, cybersecurity, and systems engineering, LHP OAS was formed to focus exclusively on extending certified intent into live environments and developed a platform, Operational Assurance Sentinel, that embodies this concept. LHP's Operational Assurance Sentinel platform delivers deterministic runtime enforcement, operational assurance scoring, and tamper-evident evidence chains that transform safety from a static milestone into a continuously verifiable discipline, enabling organizations to deploy advanced autonomous and intelligent systems with measurable, provable confidence.

Blog Series: The Death of Static Safety This is the third part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive...

Blog Series: The Death of Static Safety This is the first of a six-part guest blog series titled "The Death of Static Safety". We kick things off...
Blog Series: The Death of Static Safety This is the fifth part of a six-part guest blog series titled "The Death of Static Safety". For today's post,...
Blog Series: The Death of Static Safety This is the fourth part of a six-part guest blog series titled "The Death of Static Safety". For today's...

Construction's Software-Defined Moment This blog was originally posted by Michael Entner-Gómez on his Substack on 2/13/26.

Blog Series: The Death of Static Safety This is the sixth and final part of a guest blog series titled "The Death of Static Safety". Today, we wrap...