Why Safety Certification Assumptions Don’t Survive Reality
Blog Series: The Death of Static Safety This is the first of a six-part guest blog series titled "The Death of Static Safety". We kick things off...
3 min read
 Michael Entner-Gómez
:
Mar 4, 2026 1:01:00 PM
Michael Entner-Gómez
:
Mar 4, 2026 1:01:00 PM
This is the fourth part of a six-part guest blog series titled "The Death of Static Safety". For today's post, we'll explore how to operationalize continuous assurance without slowing the machine. But first, if you haven't read our first three posts on this overall series, we invite you to do so below. Let's go!
Part 1. Why Safety Certification Assumptions Don’t Survive Reality
Part 2. Validating Operational Assurance as a Safety Mechanism
By now, the problem should be clear. In software-defined machines, safety failures are rare because certification was incorrect. It fails because certified intent is not actively sustained as systems evolve.
Continuous assurance is the answer, but only if it can be operationalized without slowing development, deployment, or operations. That is where most organizations struggle.
The instinctive response to assurance drift is procedural: add reviews, add documentation, add approval gates. In software-defined environments, this approach does not scale. When assurance depends on manual controls, teams either slow down delivery or quietly work around the process. Neither outcome improves safety.
What is missing is not rigor, but structure.
Continuous assurance starts with treating safety intent as something living, not static. The performance bounds (SOTIF) and fault-tolerance requirements (FuSa) must be explicit, traceable, and visible. When software changes behavior, assurance must be reassessed deliberately, not reconstructed after the fact. When safety intent lives only in documents, it cannot be defended at runtime.
 The Maturity Scale defines the transition from reactive safety monitoring to an enterprise-wide culture of continuous vigilance.
The Maturity Scale defines the transition from reactive safety monitoring to an enterprise-wide culture of continuous vigilance.
Operationalizing continuous assurance is less about tools and more about how responsibility is distributed. High-performing organizations make safety boundaries clear, define which changes matter, and align product, software, and safety leadership around shared assurance signals.
This clarity reduces friction. Teams move faster when they understand where flexibility exists and where it does not. This structure preserves Freedom from Interference by ensuring that rapid software iterations in non-safety domains cannot silently compromise the enforcement signals.
The most important shift is moving from historical confidence to real-time alignment. The relevant question is no longer whether a system has ever been certified, but whether it is operating in accordance with its certified intent right now.
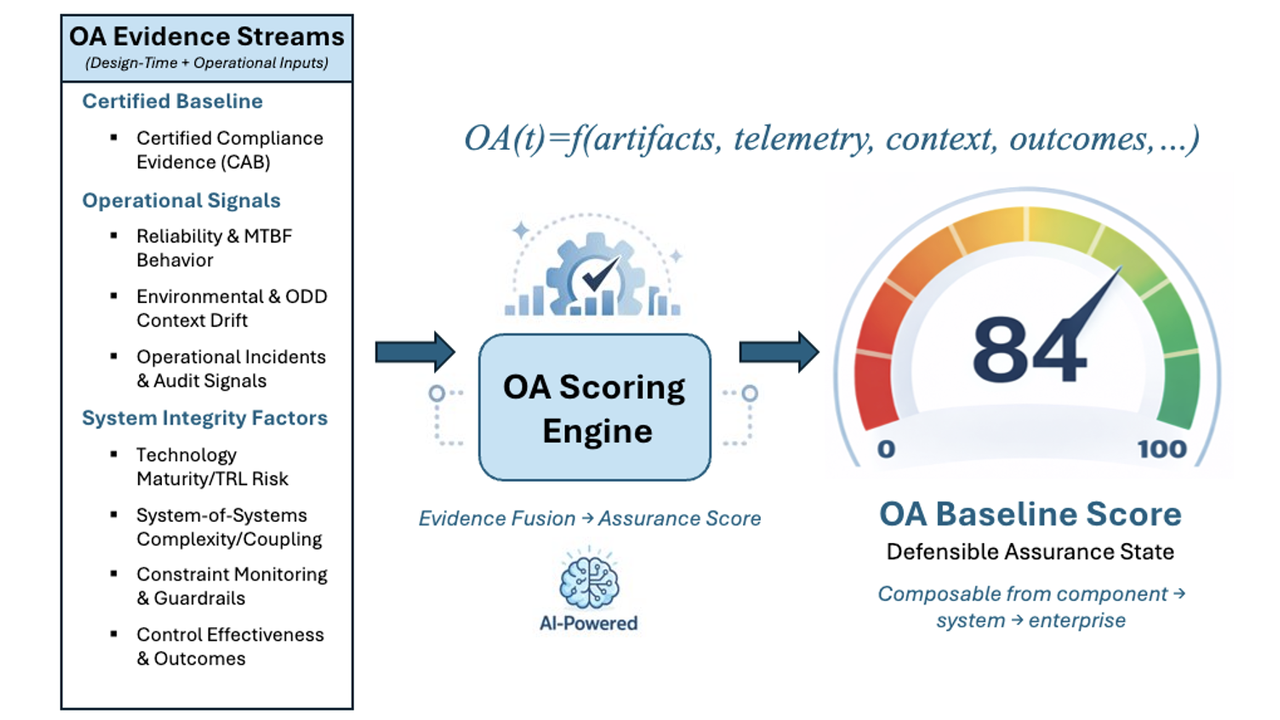
That requires visibility into a small set of safety-relevant signals, such as:
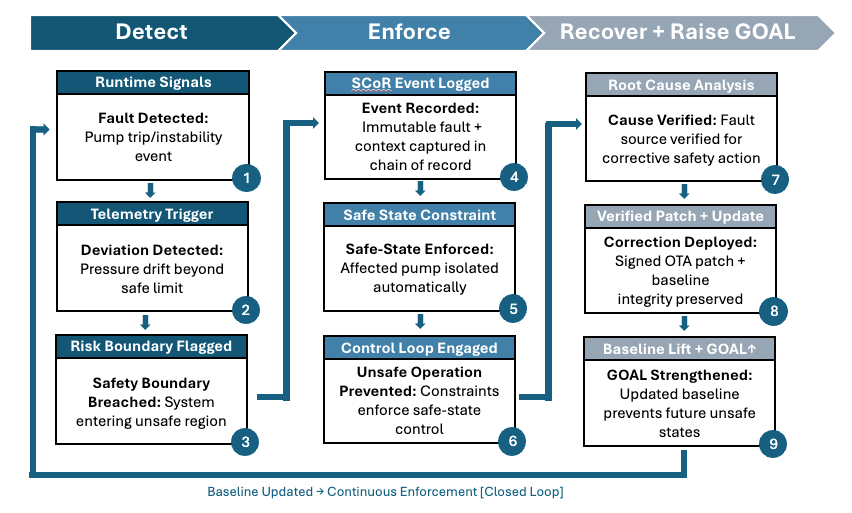
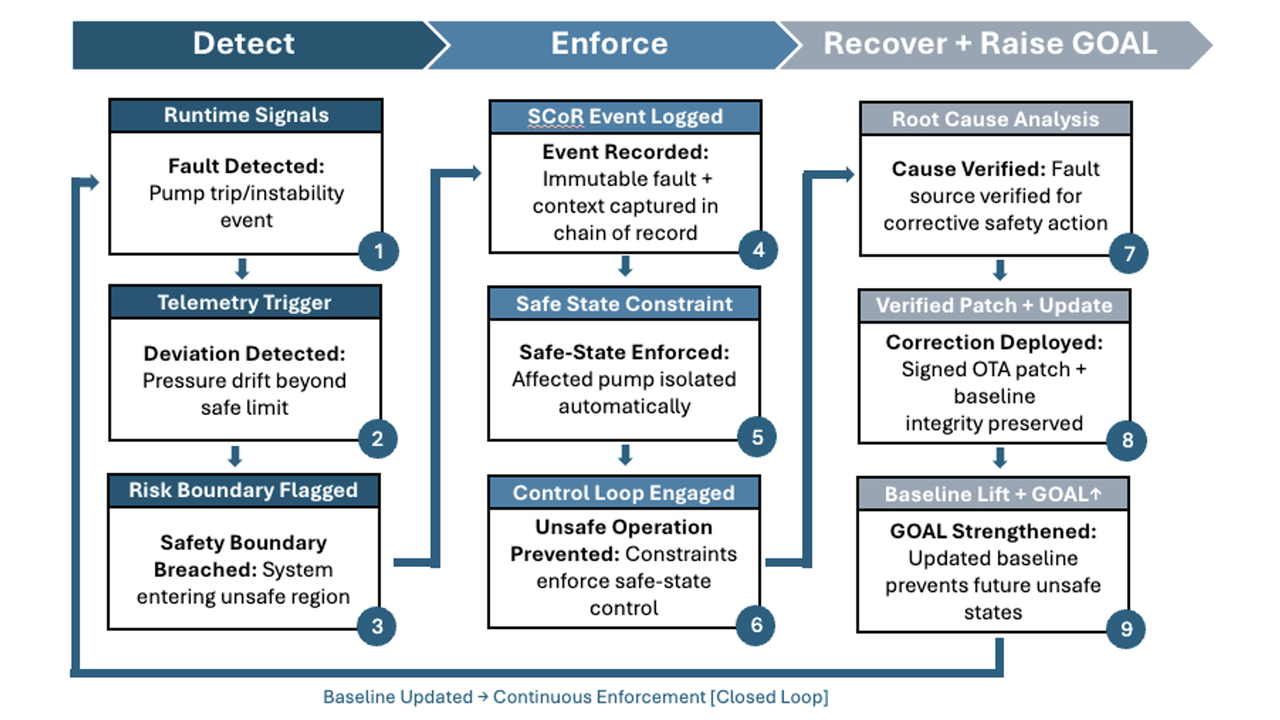
The operational workflow of a closed-loop enforcement system, mapping how runtime data triggers deterministic safety transitions.
This is not about monitoring everything. It is about watching what matters.
The goal is not to replace functional safety standards, but to make them viable in environments where machines evolve continuously. Organizations that succeed anchor on certified intent, maintain alignment as systems change, and intervene early when drift appears.
Continuous assurance is not a project or an audit. It is an operating capability. When done well, it enables faster, more confident change, clearer accountability, and stronger defensibility in the event of incidents.
The next question is not whether continuous assurance is necessary, but where your organization stands today and how much assurance has already drifted.
That is the conversation that must come next.
LHP Operational Assurance Systems (OAS) was spun out of LHP Engineering Solutions to address a growing gap in safety-critical, software-defined systems: certification at launch no longer guarantees safe operation over time. As complex platforms began receiving continuous software updates and evolving functionality, LHP OAS recognized that traditional "certify-once" models could not prevent runtime drift between validated safety intent and real-world behavior. Drawing on decades of leadership in functional safety, cybersecurity, and systems engineering, LHP OAS was formed to focus exclusively on extending certified intent into live environments and developed a platform, Operational Assurance Sentinel, that embodies this concept. LHP's Operational Assurance Sentinel platform delivers deterministic runtime enforcement, operational assurance scoring, and tamper-evident evidence chains that transform safety from a static milestone into a continuously verifiable discipline, enabling organizations to deploy advanced autonomous and intelligent systems with measurable, provable confidence.

Blog Series: The Death of Static Safety This is the first of a six-part guest blog series titled "The Death of Static Safety". We kick things off...

Blog Series: The Death of Static Safety This is the third part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive...

Blog Series: The Death of Static Safety This is the second part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive...
Blog Series: The Death of Static Safety This is the fifth part of a six-part guest blog series titled "The Death of Static Safety". For today's post,...

Blog Series: The Death of Static Safety This is the sixth and final part of a guest blog series titled "The Death of Static Safety". Today, we wrap...

Construction's Software-Defined Moment This blog was originally posted by Michael Entner-Gómez on his Substack on 2/13/26.