Keeping the Safety Case Alive: Extending Certification into Runtime
Blog Series: The Death of Static Safety This is the sixth and final part of a guest blog series titled "The Death of Static Safety". Today, we wrap...
3 min read
 Michael Entner-Gómez
:
Mar 9, 2026 9:02:00 AM
Michael Entner-Gómez
:
Mar 9, 2026 9:02:00 AM
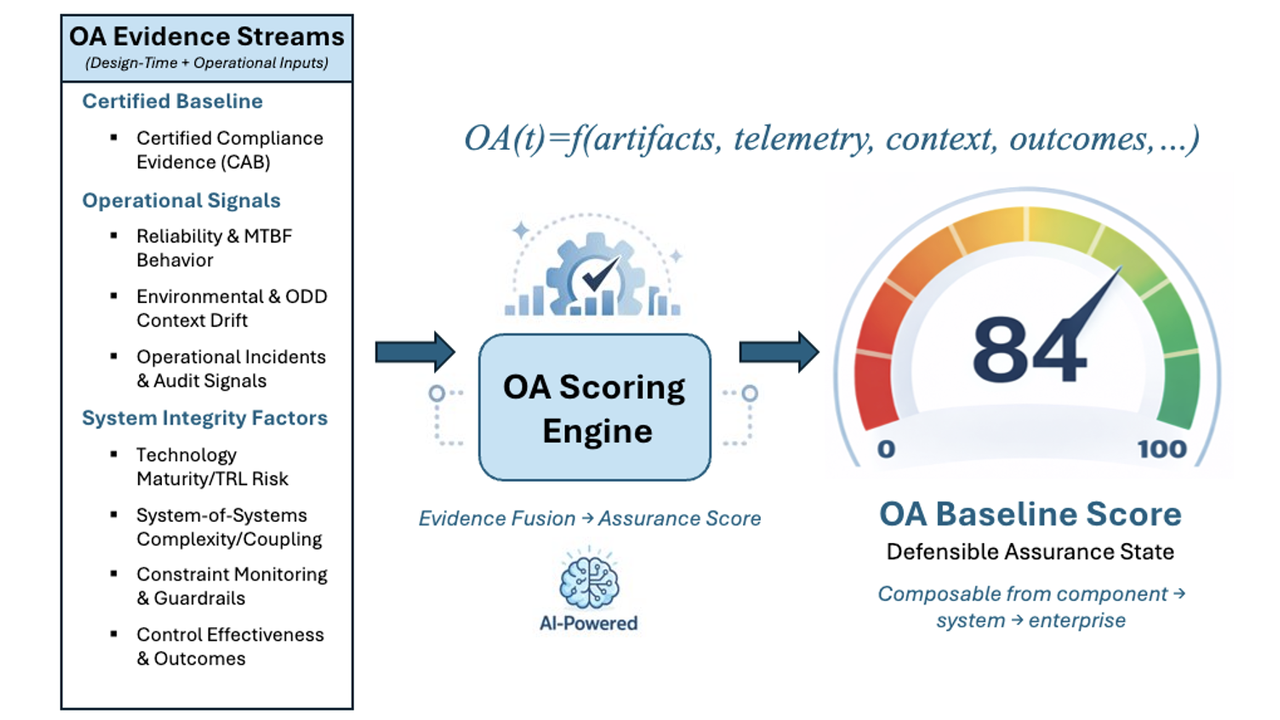
Table of Contents
This is the fifth part of a six-part guest blog series titled "The Death of Static Safety". For today's post, we're jumping right in with when safety enforcement becomes control, preventing unsafe interventions. But first, if you haven't read any of the first four articles, we invite you to do so by following these links. Let's jump in!
Part 1. Why Safety Certification Assumptions Don’t Survive Reality
Part 2. Validating Operational Assurance as a Safety Mechanism
Operational assurance is often framed as protective. It monitors. It constrains. It intervenes when risk rises. After validation and architectural decomposition, it can feel as though the safety problem has been solved.
It has not.
There is a final and critical failure mode that must be addressed directly: enforcement itself can introduce hazards.
Any action that constrains, overrides, or transitions system behavior is a control action. From a safety perspective, it does not matter whether that action originates in a planner, a controller, or an assurance mechanism. The effect on the system is the same.
This distinction is frequently overlooked because enforcement is described as conservative or protective. But protection does not eliminate risk. It redistributes it.
Triggering a fallback due to functional insufficiency, such as sensor glare or an unmapped ODD boundary, is a control action. If those changes are not carefully analyzed, they can create new hazards even as they mitigate others.
Treating enforcement as inherently safe because it is conservative is a mistake.
Systems-Theoretic Process Analysis makes this explicit. A control action can be unsafe if it is applied when it should not be, withheld when it should be applied, applied too early or too late, or applied for the wrong duration.
Enforcement actions meet every criterion.
A forced disengagement in dense traffic, a sudden capability reduction at high speed, or an unexpected transition that confuses the human driver can all increase risk. In each case, the enforcement action itself becomes part of the hazard scenario.
If enforcement logic is not analyzed as a control function, it becomes an unexamined control path.
One of the most persistent myths in safety engineering is that conservative actions are always safe actions. In practice, “safe shutdown” is not a universal solution. It is context-dependent.
What is safe at low speed may be unsafe at highway speed. What is safe in light traffic may be unsafe in congestion. What is safe for an attentive driver may be unsafe if the driver has been out of the loop.
An enforcement action that is correct in isolation can be hazardous in context. Repeated or poorly timed interventions can destabilize the system or overwhelm the human operator.
Safety is not defined by how quickly a system stops. It is defined by whether the system transitions into an operational state that has been shown to be acceptably safe.
A safe state is not a theoretical construct. It is an operational condition that has been analyzed, validated, and certified for specific contexts.
This means enforcement actions cannot be generic. Uncertainty-driven disengagement (a core SOTIF challenge) is not a universal safety strategy; it is an admission that the safe operational states were never fully defined. It is a transition that must be analyzed for secondary hazards.
Every enforcement action must be explicitly linked to a hazard identified in the Hazard Analysis and Risk Assessment. The link must explain why that specific action reduces risk in that specific context, including secondary hazards introduced by the transition itself.
Operational assurance must therefore be context-aware in how it enforces constraints. It must know not only when to intervene, but how to intervene safely.
Once enforcement is recognized as control, the implications are straightforward.
Enforcement logic must undergo the same level of safety analysis as any other controller. Unsafe control actions must be identified. Causal scenarios must be analyzed. Interactions with other safety mechanisms must be examined.
Intent is not evidence. Conservative design intent does not eliminate the need for analysis. Only demonstrated behavior does.
If enforcement actions can introduce new hazards, they must be redesigned, not excused.
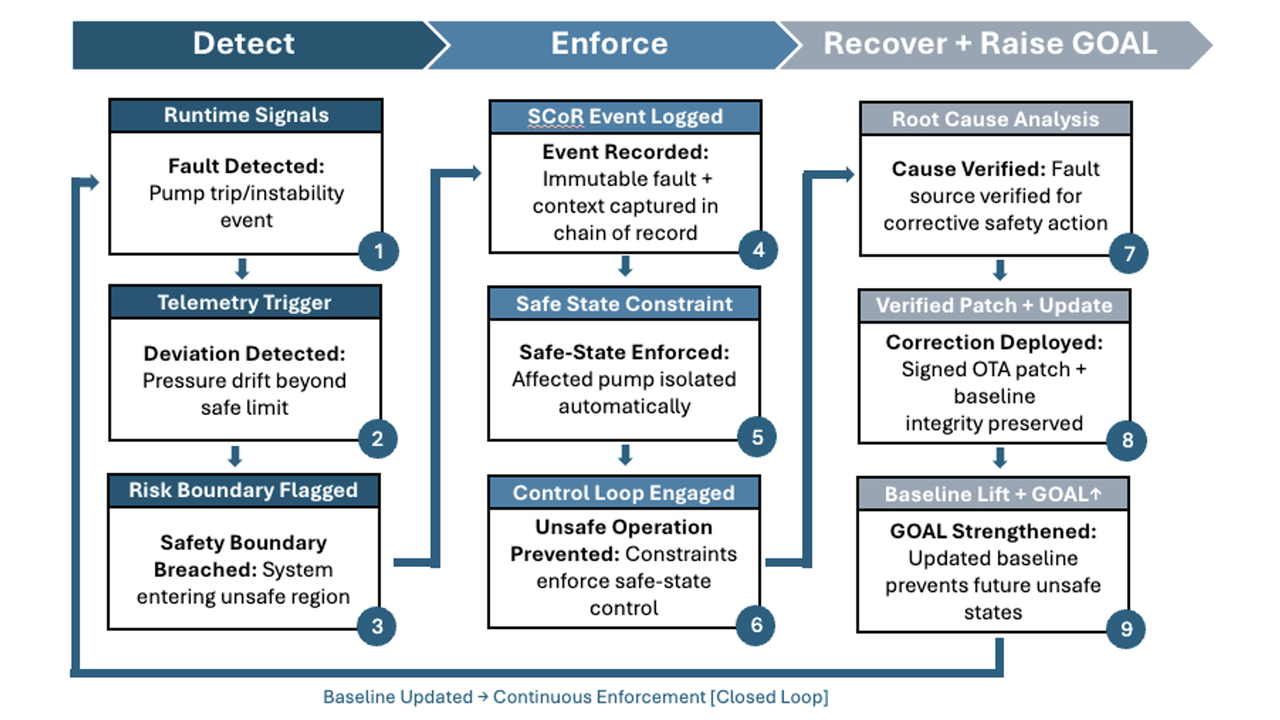
 The enforcement engine logic shows how safety-analyzed interventions are triggered by specific risk thresholds.
The enforcement engine logic shows how safety-analyzed interventions are triggered by specific risk thresholds.
Operational assurance is not about stopping the system at the first sign of uncertainty. It is about maintaining operation within validated safety boundaries and transitioning only into operational states that have been shown to be safe.
When enforcement logic creates risk, the answer is not to weaken assurance. It is to engineer it properly.
In the final article of this series, the focus shifts to the full picture. Operational assurance does not replace the safety case. It is the mechanism that keeps the original safety case valid after deployment.
LHP Operational Assurance Systems (OAS) was spun out of LHP Engineering Solutions to address a growing gap in safety-critical, software-defined systems: certification at launch no longer guarantees safe operation over time. As complex platforms began receiving continuous software updates and evolving functionality, LHP OAS recognized that traditional "certify-once" models could not prevent runtime drift between validated safety intent and real-world behavior. Drawing on decades of leadership in functional safety, cybersecurity, and systems engineering, LHP OAS was formed to focus exclusively on extending certified intent into live environments and developed a platform, Operational Assurance Sentinel, that embodies this concept. LHP's Operational Assurance Sentinel platform delivers deterministic runtime enforcement, operational assurance scoring, and tamper-evident evidence chains that transform safety from a static milestone into a continuously verifiable discipline, enabling organizations to deploy advanced autonomous and intelligent systems with measurable, provable confidence.

Blog Series: The Death of Static Safety This is the sixth and final part of a guest blog series titled "The Death of Static Safety". Today, we wrap...

Blog Series: The Death of Static Safety This is the third part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive...

Blog Series: The Death of Static Safety This is the first of a six-part guest blog series titled "The Death of Static Safety". We kick things off...
Blog Series: The Death of Static Safety This is the fourth part of a six-part guest blog series titled "The Death of Static Safety". For today's...

Blog Series: The Death of Static Safety This is the second part of a six-part guest blog series titled "The Death of Static Safety". Today, we dive...

Construction's Software-Defined Moment This blog was originally posted by Michael Entner-Gómez on his Substack on 2/13/26.